Real-time cybersecurity has become a pillar of business survival in the age of digital transformation, when business operations rely on connected systems to a significant degree. Threats do not hit one time and go away; they change, develop, and frequently even lie in the open. Threat monitoring has become a critical measure that needs to be conducted continuously to remain ahead of the cyber adversaries and guarantee timely detection and a quicker response. In the case of modern organisations, it is not only security but also the saving of trust, uptime, and competitive advantage.
The New Face of Cyber Threats
Cyber threats have evolved and are now more advanced, using automation, artificial intelligence, and networks of malicious players across the world. There is no longer any need to use brute force in order to attack, and there are minor vulnerabilities that attackers use in endpoints, on cloud environments, and on IoT devices. Such a dynamic threat landscape requires an active defense paradigm, which should be able to track, identify, and eliminate risks 24/7.
Key Advantages of Threat Monitoring
- 1. Real-Time Detection
Conventional security audits are conducted every now and then, yet attacks are ongoing. The constant monitoring of threats bridges that gap, where anomalies are recognized during the occurrence and instant notifications are initiated to initiate swift actions. - 2. Early Risk Identification
Monitoring the traffic, user actions, and system logs allows organizations to detect possible threats in their early stages and reduce the occurrence of losses and costs of response. - 3. Increased Visibility in the Environments
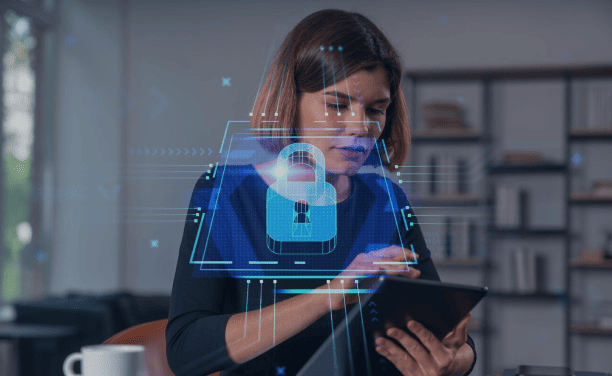
Regardless of the location of the data (on-premises, cloud, or hybrid), it is monitored to provide a single view, enabling the teams to identify the threats promptly and precisely. - 4. Regulation & Compliance Alignment
The current frameworks, such as ISO 27001, NIST, and SOC 2, consider continuous risk evaluation. Continuous monitoring helps in making audits ready and provides compliance reports through automated data logs. - 5. Shortened Reaction and Recovery time
The threat can be contained at a faster rate in case they are spotted sooner. This reduces the operational interference, maintains the service, and safeguards the business continuity.
Implementation Best Practices
In order to achieve the effectiveness of continuous monitoring, organizations need to combine high-level analytics, automated detection technologies, and human skills. This includes:
- Implementing centralized Security Information and Event Management (SIEM).
- Applying anomaly detection based on AI-based behavioral analytics.
- Installation of 24/7 monitoring functions with alarm progressions.
- Training teams in a continuous fashion to understand threat intelligence.
Being One Step Ahead of All Dangers
It is not a luxury; monitoring of threats is a business necessity. In the modern expeditious cyberspace, threats are developed at a quicker pace than even manual procedures can follow. The agility of organizations to respond before damage is done is the advantage of continuous monitoring, where the security posture of an organization changes with the rising risks. The result? A stronger, more trusted, and future viable organization.